Sublime
An inspiration engine for ideas
Condorman • A Conceptual View of a UAP Reverse Engineering Program
After Action Report: CAPS 2024
AAR
Please create an after action report and recommendations with the following notes on the CAPS exercise as well as aggregate the survey answers together
Section 1: Account Takeovers and Unauthorized Funds Transfers
Scenario Pt 1: Several High-Value Customers have been targeted by Spear Phishing attacks via email,
... See more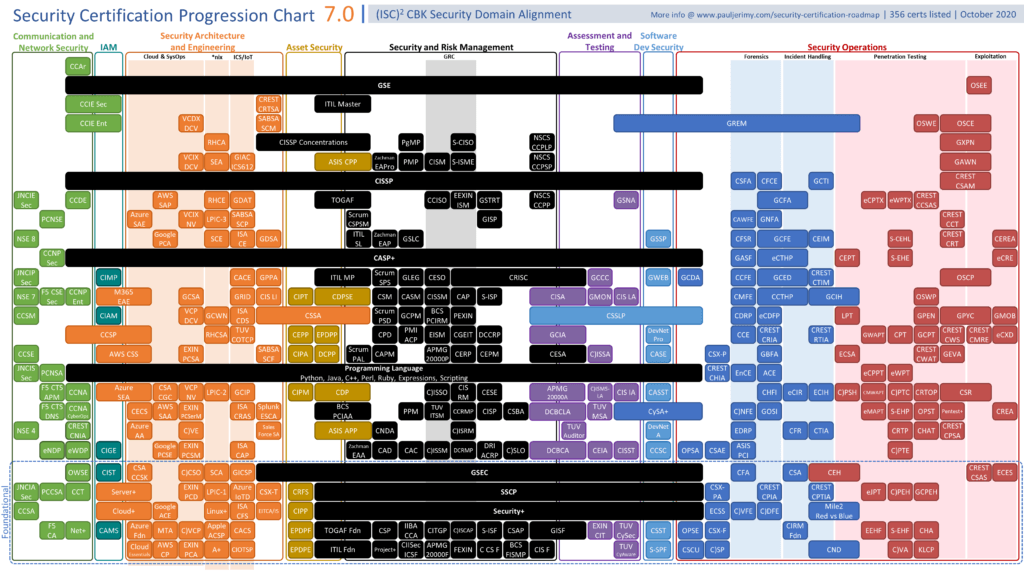
AH and ESP can be used together or separately, but only ESP can provide encryption (confidentiality). When two routers want to communicate over IPSec, they must first agree on a number of options such as hashing algorithms, encryption algorithms, tunnel modes, etc. When a router receives these parameters, they are stored in a security association
... See morePhil Martin • Simple CISSP
It went without saying that breaches of this secrecy would result in excommunication from future meetings. When a breach did occur, the Kochs launched an intense weeklong internal investigation to identify and plug the leak.